Cyberstalking
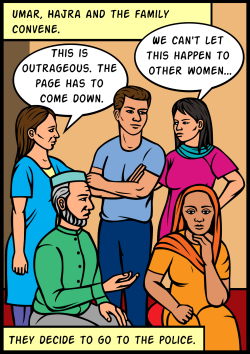
Cyberstalking is a technologically-based attack on a person for reasons of anger, revenge or control.
A Working to Halt Online Abuse report covering 2000-2013 reveals that half of the respondents were cyberstalked by someone they had some sort of relationship with, while the other half had never had any relationship with the perpetrator. Of the former, the most common connection was an ex (39.5%), followed by an online acquaintance (16.25%) and a friend (12.5%).
Women are much more likely than men to experience stalking, especially by an intimate partner. Most of those stalked by an intimate partner also face physical assault from that person.
Cyberstalking includes but is not limited to:
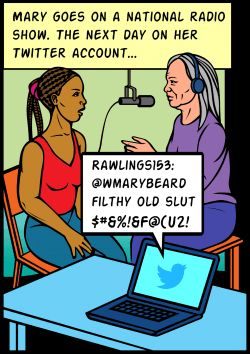
harassment, humiliation and embarrassment of the person targeted
harassing family, friends and employers to isolate the person
tactics to make the target fearful
taking on the identity of the other person
monitoring (e.g., using Facebook notifications to find out where the person is going, using spy ware, activating GPS)
Cyberstalking can be difficult to address due to:
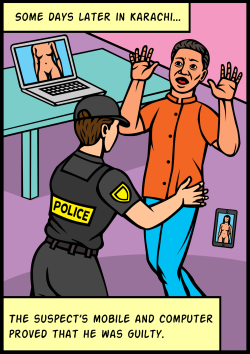
stalker anonymity
law enforcement assumption that a stalker located far away will not travel to follow up on threats
the stalker encouraging online buddies to participate in the harassment, increasing the person's distress
How people experience cyberstalking
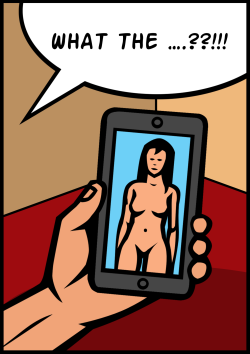
Mobile phones
Connections
Wifi hotspots and bluetooth connections can reveal your location and make it easier for people to hack your phone.
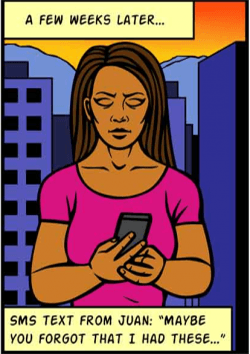
SMS / Calls: If a stalker can obtain your mobile number, they may harass you through SMS messages and phone calls. They may use it in combination with GPS to reveal that they know your location. Stalkers can also use spyware to intercept your messages and calls.
Passwords
If your phone is not password protected, anyone who gets their hands on it can access your information. Password hacking is common, and the more a stalker knows about you, the more likely they are to guess your passwords. Plus, the most common passwords are easy to guess, such as "password", "123456", and "letmein".
GPS
GPS may tell you what coffee shops are nearby, but it can also let others know where you are. The fortunately defunct Girls Around Me app was a perfect storm of GPS info and unscrupulous developers.
Photos: Photos have information embedded in their properties that include when and where you took them. It can also be possible to decipher the location based on what's in the image.
Applications
Malicious apps may contain spyware. The more capabilities your smartphone has, like GPS, the more those extras can be used to spy on you.

Laptops
Passwords
If your device is not password protected, anyone who gets their hands on it can access your information. Password hacking is common, and the more a stalker knows about you, the more likely they are to guess your password. Plus, the most common passwords are easy to guess, such as "password", "123456", and "letmein".
Connections
Wifi hotspots and bluetooth connections can reveal your location and make it easier for people to hack your device
Webcams
Stalkers use spyware to access webcams and film people without their knowledge or consent.
Blogs
Stalkers like to hang out in comment spaces and post threats and insults. This is especially common when the stalker is someone unknown to you.
Social Media
It's very easy to glean information about where you live, the places you visit regularly, and the people you care about from posts and pictures. Your friends might also unintentionally reveal information about you.
Email addresses are often attached to real names and profiles, and stalkers may use these to contact you directly. Again, spyware can be used to access your private email.
Online Chatting
Stalking from online acquaintances can happen in chatrooms. Also, if you use the option to "automatically remember your password", anyone using your computer can log into your messenger services.
| Attachment | Size |
|---|---|
| Know More About Cyberstalking | 6.97 MB |